I gave a talk in the Netherlands last week about the future of technology. I’m gathering together a few resources here for attendees. Even if you didn’t attend, you may still find these interesting, although some of the context will be lost.
Previous Articles
I’ve written a handful of articles on these topics in the past. Below are three that I think are relevant:
- How to Predict the Future (my article covering the first portion of the talk)
- The Future of Transportation (an article I wrote that extrapolates trends to look at the next 20 years)
- The Future of Robotics and Open Source is Open (an article about why open source and cheap hardware is fueling an acceleration of AI/robotics development)
Next Ten Years
- Crystal Email Analysis and Improvement Plugin
- IBM Verse: Business email with social features
- The Phoenix Project: A Novel about IT, DevOps, and Helping Your Business Win
- Amazon Warehouse Robots Video with Kiva robots
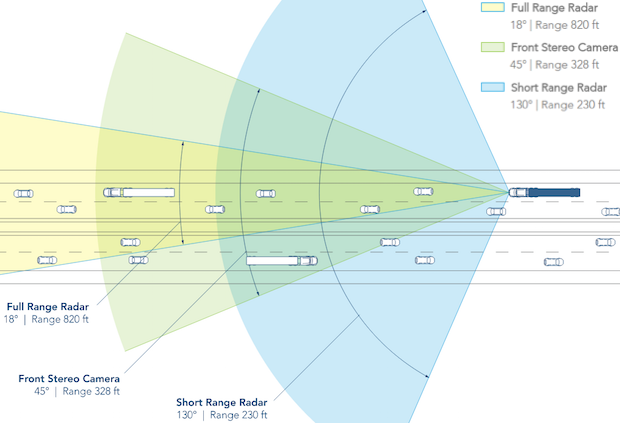
- Autonomous vehicle intersection video (more detailed version that explains how it works)
- The Acceleration of Acceleration: How The Future Is Arriving Far Faster Than Expected
Ten to Thirty Years
- How the Tesla Model S is Made (video showing robotic Tesla factory)
- I didn’t have time to discuss it, but lights-out manufacturing is also an interesting development.
- Virtual Arms Neural Implant Monkey research
- Argus II retinal prosthesis (wikipedia)
- The Singularity is Near, Ray Kurzweil’s very optimistic book about accelerating technology, artificial intelligence, transhumanism.
- Our Final Invention, James Barrat’s book about the dangers of artificial intelligence